This website uses cookies. By clicking Accept, you consent to the use of cookies. Click Here to learn more about how we use cookies.
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
- Extreme Networks
- Community List
- Network Management & Authentication
- ExtremeCloud IQ- Site Engine Management Center
- XMC - User Group with only read-only access to som...
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
XMC - User Group with only read-only access to some devices
XMC - User Group with only read-only access to some devices
Options
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Get Direct Link
- Report Inappropriate Content
03-12-2019 02:45 PM
Hi,
i'm actually designing user right to device in xmc 8.2.
For the example, the user "DIT" should be able to have full right on certain devices and only read-only right to certain other device.
I created a local user "DIT" in a specific user-group "DIT_LILLE" with standard netsight right (allow set snmp to devices is checked)
I created 2 profiles :
Both of the device have a default administration profile set to the RW profile.
When I log on with the "DIT" user, I can make change to interface status and i can enforce device configuration on both device so the RO profile seems to not being used ...
If I uncheck the ''allow set snmp to device'', the user is unable to make change to both devices.
So it seems that the user "DIT" is using the administration profile set globally to the devices instead of the specific one made in the device-mapping .
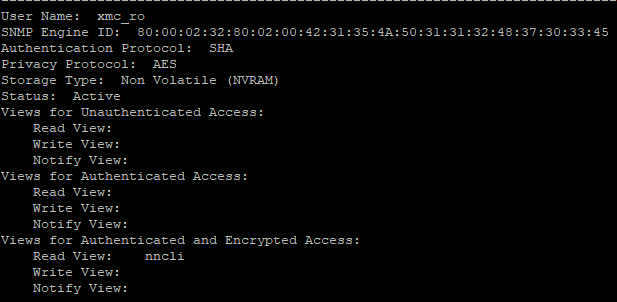
here is the SNMPv3 user configuration on the device:
I made a tcpdump of a disable port sent to the read-only device and I can see that XMC didn't use the specific SNMPv3 user xmc_ro but the RW one xmc.
16:22:35.659049 IP pns1scmgb001.prod-exp.justice.fr.39111 > 10.79.252.245.snmp: F=apr U="xmc" [!scoped PDU]83_54_9e_aa_11_f9_05_7d_8d_84_20_77_f0_f8_32_27_10_a8_f4_e5_a4_aa_71_e3_25_0c_49_a9_2c_33_c1_fa_89_c8_1a_ba_33_ac_01_f6_b3_62_38_e6_8e_d8_84_13_b1_c7_c7_f9_c1_64_fa_e6_01_50_16
16:22:35.671323 IP 10.79.252.245.snmp > pns1scmgb001.prod-exp.justice.fr.39111: F=ap U="xmc" [!scoped PDU]92_e9_b2_94_6f_89_f9_87_2f_cb_f8_ab_0a_f9_f9_92_f3_7e_38_be_3e_3e_04_39_2d_5e_c7_4a_d2_96_fe_cc_0c_49_ba_e9_2e_cc_54_b5_9f_05_c4_1b_da_12_26_48_08_18_1f_f7_12_13_af_ef_53_a9_f0
Is there someone here that managed to deal with this ?
thanks!
i'm actually designing user right to device in xmc 8.2.
For the example, the user "DIT" should be able to have full right on certain devices and only read-only right to certain other device.
I created a local user "DIT" in a specific user-group "DIT_LILLE" with standard netsight right (allow set snmp to devices is checked)
I created 2 profiles :
- the first profile (RW) have Read-write CLI and Read-write SNMP credentials (SNMPv3)
- the second profile (RO) have read-only CLI and read-only SNMP credentials (SNMPv3)
Both of the device have a default administration profile set to the RW profile.
When I log on with the "DIT" user, I can make change to interface status and i can enforce device configuration on both device so the RO profile seems to not being used ...
If I uncheck the ''allow set snmp to device'', the user is unable to make change to both devices.
So it seems that the user "DIT" is using the administration profile set globally to the devices instead of the specific one made in the device-mapping .
here is the SNMPv3 user configuration on the device:
I made a tcpdump of a disable port sent to the read-only device and I can see that XMC didn't use the specific SNMPv3 user xmc_ro but the RW one xmc.
16:22:35.659049 IP pns1scmgb001.prod-exp.justice.fr.39111 > 10.79.252.245.snmp: F=apr U="xmc" [!scoped PDU]83_54_9e_aa_11_f9_05_7d_8d_84_20_77_f0_f8_32_27_10_a8_f4_e5_a4_aa_71_e3_25_0c_49_a9_2c_33_c1_fa_89_c8_1a_ba_33_ac_01_f6_b3_62_38_e6_8e_d8_84_13_b1_c7_c7_f9_c1_64_fa_e6_01_50_16
16:22:35.671323 IP 10.79.252.245.snmp > pns1scmgb001.prod-exp.justice.fr.39111: F=ap U="xmc" [!scoped PDU]92_e9_b2_94_6f_89_f9_87_2f_cb_f8_ab_0a_f9_f9_92_f3_7e_38_be_3e_3e_04_39_2d_5e_c7_4a_d2_96_fe_cc_0c_49_ba_e9_2e_cc_54_b5_9f_05_c4_1b_da_12_26_48_08_18_1f_f7_12_13_af_ef_53_a9_f0
Is there someone here that managed to deal with this ?
thanks!
0 REPLIES 0