This website uses cookies. By clicking Accept, you consent to the use of cookies. Click Here to learn more about how we use cookies.
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
- Extreme Networks
- Community List
- Technical Discussions
- Network Architecture & Design
- RE: Help with an MPLS/OSPF architecture
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Help with an MPLS/OSPF architecture
Help with an MPLS/OSPF architecture
Options
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Get Direct Link
- Report Inappropriate Content
09-19-2018 04:06 PM
Hi dears,
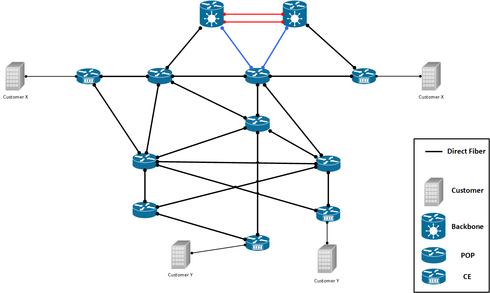
I would like a help with the architecture displayed below. Please feel free to make any comment.
Network descriptions and requirements
- It's a metro network that have the goal to connect several locations;
- It's works like a big intranet, then there's no need the traffic isolation (VPN L3);
- Today, the network runs OSPF and have about 91 areas and 200 routers;
- The picture below shows a network summary. Each router has at least to another two routers connected;
- The customer router has two connections too;
- The backbone routers are connected to POP routers, but there are customer routers directly connected too;
- The POP routers connected to backbone routers are
part of Area 0. They are connected in another POPs and to customers too.
Reasons to implement MPLS
- Traffic Engineer
- VPWS and VPLS;
- QoS and better resource utilization;
- Picture below shows the scenario wanted:
Notes:
- There're no plan to use VPN to isolate some customer traffic because one network requirement is connect all customer via L3 . Is it worth implementing BGP?
- I think that implement iBGP will increase the network complexity.
Thanks in advance for all!
I would like a help with the architecture displayed below. Please feel free to make any comment.
Network descriptions and requirements
- It's a metro network that have the goal to connect several locations;
- It's works like a big intranet, then there's no need the traffic isolation (VPN L3);
- Today, the network runs OSPF and have about 91 areas and 200 routers;
- The picture below shows a network summary. Each router has at least to another two routers connected;
- The customer router has two connections too;
- The backbone routers are connected to POP routers, but there are customer routers directly connected too;
- The POP routers connected to backbone routers are
part of Area 0. They are connected in another POPs and to customers too.
Reasons to implement MPLS
- Traffic Engineer
- VPWS and VPLS;
- QoS and better resource utilization;
- Picture below shows the scenario wanted:
Notes:
- There're no plan to use VPN to isolate some customer traffic because one network requirement is connect all customer via L3 . Is it worth implementing BGP?
- I think that implement iBGP will increase the network complexity.
Thanks in advance for all!
12 REPLIES 12
Options
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Get Direct Link
- Report Inappropriate Content
09-19-2018 09:09 PM
Have you thought about Fabric Connect? Extreme added some extensions to SPBM 802.1aq to allow SPB to support L3(VRFs) and native Multicast support (no need for PIM).
FC (Fabric Connect) would have no issue with the Topology (Ring, Mesh, partial mesh all possible)
FC can easily extend layer 2 or layer 3 VSNs (VPNs) between sites (or anywhere you need them), different Tenants can even use the same L3 IP address scheme
FC uses something called transparent UNI to accomplish a true L2 pseudo wire (Layer 2 control protocols do pass, just not ethernet pause frames) (It is edge port to edge port, truly a point to point L2 connection thru the fabric, between any 2 edge points in the fabric)
FC can easily extend a VLAN or a subnet anywhere in the Fabric, there are 16million ISIDs (individual services) that can be created, and remain completely separated because of the PBB 802.11ah header escape that happens as frame ingress into the Fabric
FC handles multicast better than just about anything else out there, no need for PIM
With FC, all redundant links can be used with no fear of loops, IS-IS is used to populate the FDB, there is no flooding and learning or broadcasting in the Backbone (Core)
Traffic engineering could be done by manipulating the ISIDs manually to determine which traffic (ISIDs) traverses which links (i am not exactly sure how, but that is why multiple BVIDs are used, to create multiple ECT (equal cost trees)
FC would classify at the edge and then use COS in the outer header for QOS in the backbone.
Extreme Fabric connect can scale to around 1000 FC nodes all in the same 'Area' or level, I believe IS-IS uses level 1 or level 2 instead of area's, so no need to configure inter-area routing and IS-IS in FC runs on Ethernet, not IP, so there are no issues with IP address on backbone core bridges, and there is not supposed to be any way to have asynchronous routing because all of the routes (Trees) are agreed upon by all nodes in the path (asynchronous routing can happen in inter-area OSPF), being in the same IS-IS level all nodes have direct link state knowledge of each other, whereas with inter-area OSPF, routers in different area's do not have direct knowledge and rely on summaries from the ABRS.
How are all the sites connected ? (Dark Fiber, Metro E ...)
FC can use Fabric Extend at Layer 2 (BVIDs) or Layer 3 (using VXLAN) to traverse no fabric nodes or segments.
Just food for thought, FC is not right for every scenario.
Jake
FC (Fabric Connect) would have no issue with the Topology (Ring, Mesh, partial mesh all possible)
FC can easily extend layer 2 or layer 3 VSNs (VPNs) between sites (or anywhere you need them), different Tenants can even use the same L3 IP address scheme
FC uses something called transparent UNI to accomplish a true L2 pseudo wire (Layer 2 control protocols do pass, just not ethernet pause frames) (It is edge port to edge port, truly a point to point L2 connection thru the fabric, between any 2 edge points in the fabric)
FC can easily extend a VLAN or a subnet anywhere in the Fabric, there are 16million ISIDs (individual services) that can be created, and remain completely separated because of the PBB 802.11ah header escape that happens as frame ingress into the Fabric
FC handles multicast better than just about anything else out there, no need for PIM
With FC, all redundant links can be used with no fear of loops, IS-IS is used to populate the FDB, there is no flooding and learning or broadcasting in the Backbone (Core)
Traffic engineering could be done by manipulating the ISIDs manually to determine which traffic (ISIDs) traverses which links (i am not exactly sure how, but that is why multiple BVIDs are used, to create multiple ECT (equal cost trees)
FC would classify at the edge and then use COS in the outer header for QOS in the backbone.
Extreme Fabric connect can scale to around 1000 FC nodes all in the same 'Area' or level, I believe IS-IS uses level 1 or level 2 instead of area's, so no need to configure inter-area routing and IS-IS in FC runs on Ethernet, not IP, so there are no issues with IP address on backbone core bridges, and there is not supposed to be any way to have asynchronous routing because all of the routes (Trees) are agreed upon by all nodes in the path (asynchronous routing can happen in inter-area OSPF), being in the same IS-IS level all nodes have direct link state knowledge of each other, whereas with inter-area OSPF, routers in different area's do not have direct knowledge and rely on summaries from the ABRS.
How are all the sites connected ? (Dark Fiber, Metro E ...)
FC can use Fabric Extend at Layer 2 (BVIDs) or Layer 3 (using VXLAN) to traverse no fabric nodes or segments.
Just food for thought, FC is not right for every scenario.
Jake
Options
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Get Direct Link
- Report Inappropriate Content
09-19-2018 09:09 PM
Jake, you're right, Extreme introduces additional TLVs for IS-IS control plane in terms of L3 virtualized services and multicast traversal over SPB backbone.
The main differences:
- L2 VSN: on SPB edge devices (BEBs) you just map VLANs or ports or port+VLAN to a service identifier (I-SID)
- L3 VSN: on BEBs you map VRFs to an I-SID
- L2 VSN: entire L2 frame is being encapsulated with MAC-in-MAC
- L3 VSN: L2 header (CMAC) from a tenant frame is null as it's outside scope of interest (as it is with routers, right? but here it's just one big router formed by the backbone)
- L2 VSN: standard IS-IS TLVs are used to exchange information between backbone nodes about BEBs that serve the same I-SIDs
- L3 VSN: proprietary (so far, it's a proposal to enhance the standard I believe) IS-IS TLVs are used to advertise route reachability between VRFs that serve the same I-SID
SPBM is something really interesting, however, as you can see there are plenty of mechanisms on the market right now. All those MPLS/VPLS/etc., and within Extreme couple of fabric-like solutions... there's a lot of options from which you can choose what fits you the most. 🙂
Regards,
Tomasz
The main differences:
- L2 VSN: on SPB edge devices (BEBs) you just map VLANs or ports or port+VLAN to a service identifier (I-SID)
- L3 VSN: on BEBs you map VRFs to an I-SID
- L2 VSN: entire L2 frame is being encapsulated with MAC-in-MAC
- L3 VSN: L2 header (CMAC) from a tenant frame is null as it's outside scope of interest (as it is with routers, right? but here it's just one big router formed by the backbone)
- L2 VSN: standard IS-IS TLVs are used to exchange information between backbone nodes about BEBs that serve the same I-SIDs
- L3 VSN: proprietary (so far, it's a proposal to enhance the standard I believe) IS-IS TLVs are used to advertise route reachability between VRFs that serve the same I-SID
SPBM is something really interesting, however, as you can see there are plenty of mechanisms on the market right now. All those MPLS/VPLS/etc., and within Extreme couple of fabric-like solutions... there's a lot of options from which you can choose what fits you the most. 🙂
Regards,
Tomasz
Options
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Get Direct Link
- Report Inappropriate Content
09-19-2018 09:09 PM
Extreme Fabric connect uses standard SPBM for L2 VSNs and for L3 it uses some custom extensions to IS-IS (I believe) ... the L3 VSN should be up for standardization.
However if you can not do the entire backbone, it is possible to phase in FC, because the VSP switches are still Layer 3 switches that can participate in OSPF and BGP... i don't believe they can do MPLS though.
good luck
Jake
However if you can not do the entire backbone, it is possible to phase in FC, because the VSP switches are still Layer 3 switches that can participate in OSPF and BGP... i don't believe they can do MPLS though.
good luck
Jake
Options
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Get Direct Link
- Report Inappropriate Content
09-19-2018 09:09 PM
Hi Jake, thank you for the attention!
I know a little bit of Fabric Connect, but I think that is like the Ethernet Fabric and is possible to have a Fabric L3, right?
These technology is awesome, but in this case I don't can standardize the network because I have a lot of equipments non-Extreme in network that support BGP/MPLS and i don't change them now. In this moment I will change the backbone because it don't suppport MPLS.
Thank you so much for your time!
I know a little bit of Fabric Connect, but I think that is like the Ethernet Fabric and is possible to have a Fabric L3, right?
These technology is awesome, but in this case I don't can standardize the network because I have a lot of equipments non-Extreme in network that support BGP/MPLS and i don't change them now. In this moment I will change the backbone because it don't suppport MPLS.
Thank you so much for your time!
Options
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Get Direct Link
- Report Inappropriate Content
09-19-2018 04:45 PM
It is a good design, but my question is: What equipment (Cisco, Extreme Switch, HP, or else) are you using for this?
This kind of design with multi tenants (Customers) is good with osfp overlay by MPLS. The MPLS will behave like a pseudo VPN with no encryption. MPLS will allow each tenant (Customer) to have his network logically seperated from others.
With BGP it possible to have the same outcome, but it very complexe. NB: Complexity is a design killer. Simplicity is better.
This kind of design with multi tenants (Customers) is good with osfp overlay by MPLS. The MPLS will behave like a pseudo VPN with no encryption. MPLS will allow each tenant (Customer) to have his network logically seperated from others.
With BGP it possible to have the same outcome, but it very complexe. NB: Complexity is a design killer. Simplicity is better.