This website uses cookies. By clicking Accept, you consent to the use of cookies. Click Here to learn more about how we use cookies.
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
- Extreme Networks
- Community List
- Network Management & Authentication
- ExtremeCloud IQ- Site Engine Management Center
- AP Aware and radius proxy troubleshooting
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
AP Aware and radius proxy troubleshooting
AP Aware and radius proxy troubleshooting
Options
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Get Direct Link
- Report Inappropriate Content
03-02-2022 09:17 PM
Hi,
I'm trying to use NAC as a proxy utilizing AP aware to forward the requests onto the NPS (I would prefer to go directly to LDAP but need to troubleshoot this first before trying a new setup).
The current setup I have is:
Notes
I'm happy to learn more and give details on anything but I'm currently going around in circles and assume I'm not aware of or overlooking something.
Thank you.
I'm trying to use NAC as a proxy utilizing AP aware to forward the requests onto the NPS (I would prefer to go directly to LDAP but need to troubleshoot this first before trying a new setup).
The current setup I have is:
- 305C AP connected to X440-G2, the X440-G2 is being managed by XIQ-SE/NAC.
- Settings for the policy = "TCI Overwrite = Enabled", "Access Control = Permit traffic", "AP Aware = Enabled", "Vlan egress = mgmt untagged and Wireless VLANs tagged"
- Port policy is successfully applying to the port by MAC-auth for the AP
- |PID |Name |RS|PVID|NSI |CoS|MIR|STDOA|T U|prec |aSum |dSum |web|
|21 |Role-WiFi-APs |A |4095|none | | | YY|YY | | |InUse| | - XOS-PoS.34 # show policy profile 21
Profile Index :21
Profile Name :Role-WiFi-APs
Row Status :active
Port VID Status :enabled
Port VID Override :4095
CoS Status :disabled
CoS :0
Web Redirect Index :0
Disable ingress port :disabled
Replace TCI Status :enabled
Auth Override Status :enabled
NSI :none
Tagged Egress :50,60-61,65-68,73
Untagged Egress :10
Forbidden Egress :
Rule Precedence :1-2,10,29,12,32,13,33,14-15,34,16,35,17,36,18,37,19,23,20-22,25,31
:MACSource (1), MACDest (2), IPv6Dest (10),
:Application (29), IPSource (12), IPSourceL4Range (32),
:IPDest (13), IPDestL4Range (33), IPFrag (14),
:UDPSrcPort (15), UDPSrcPortRange (34),
:UDPDestPort (16), UDPDestPortRange (35),
:TCPSrcPort (17), TCPSrcPortRange (36),
:TCPDestPort (18), TCPDestPortRange (37), ICMPType (19),
:ICMP6Type (23), TTL (20), IPTOS (21), IPProto (22),
:Ether (25), Port (31)
Admin Profile Usage :none
Oper Profile Usage :30
Dynamic Profile Usage :30
- |PID |Name |RS|PVID|NSI |CoS|MIR|STDOA|T U|prec |aSum |dSum |web|
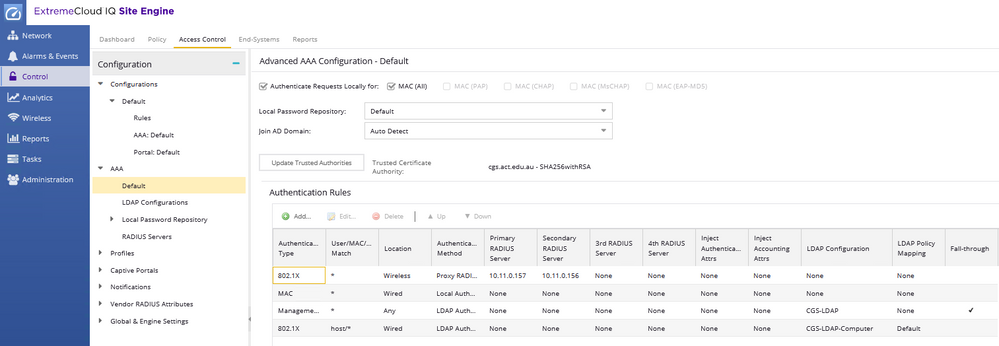
- NAC AAA Setup
- The NPS servers have had the engine IPs added as radius clients
- The NPS connection requests and Network policies remain the same as what I'm using to authenticate wireless clients directly (I'm currently not using the NAC as a proxy)
- The test AP is configured in Cloud_IQ to authenticate against the NAC engine
- They are using Filter-ID which remains the same on the test AP and NPS as the current production setup.
- The AP is added into NAC as a switch passing Cloud-IQ attribute (this part I did awhile back and could be a cause of my problems)
- I have rules to match wireless location and various user groups
- User groups are Radius user groups with Filter-ID matching both Cloud-IQ and NPS
- Access control/Netlogin is setup on the device and port level to auth 802.1x/MAC
- Currently my ZTP push is having an issue where radius settings are not being loaded
- I have manually added configuration for radius to the switch but this could be a cause.
- XOS-PoS.1 # sh configuration detail | include radius
configure radius netlogin 1 server 10.10.222.104 1812 client-ip 10.10.222.102 vr VR-Default
configure radius 1 shared-secret encrypted "#$O2iMVwWC4ZDH9JdrgqI3vzG5/6g=="
configure radius netlogin 2 server 10.10.222.105 1812 client-ip 10.10.222.102 vr VR-Default
configure radius 2 shared-secret encrypted "#$i8HhFzT4sKw4GY4/AVGdfgD68mpdg=="
configure radius-accounting netlogin 1 server 10.10.222.104 1813 client-ip 10.10.222.102 vr VR-Default
configure radius-accounting 1 shared-secret encrypted "#$DePuVDnJYgdfgpm0TuV7ksQy/5A=="
configure radius-accounting 1 timeout 10
configure radius-accounting netlogin 2 server 10.10.222.105 1813 client-ip 10.10.222.102 vr VR-Default
configure radius-accounting 2 shared-secret encrypted "#$cE4VPPI94EdfgEddX7/r0VSMawlg=="
enable radius
enable radius mgmt-access
enable radius netlogin
configure radius timeout 3
configure radius retries 3
disable radius-accounting
disable radius-accounting netlogin
configure radius-accounting mgmt-access timeout 3
configure radius-accounting netlogin timeout 3
disable radius dynamic-authorization
configure radius tls ocsp on
configure radius tls tcp-user-timeout default
configure radius authorization tokens 2
configure netlogin mac authentication database-order radius local
configure netlogin web-based authentication database-order radius local
configure netlogin dot1x radius-accounting on
- XOS-PoS.1 # sh configuration detail | include radius
- I have manually added configuration for radius to the switch but this could be a cause.
Notes
- I've had this working a couple of time while testing various configurations but both times I've tried something else and when reverting I've been unable to have it working again.
- It was last working a couple of days ago before I tried setting up LDAP direct instead. During that configuration it seemed to be stuck being unable to authenticate me, when I reverted the settings the same LDAP error persisted until I factory reset the switch and started again.
- With this configuration sh FDB didn't have a MAC associated this morning, it has stayed on there after doing various changes today (I was still able to ping the AP)
- I'm able to use the AP directly to NPS when changing the Cloud-IQ Radius servers and removing AP Aware
- Nothing is seen in the switch logs on this setup when devices try to authenticate on wireless (I'm assuming this is correct since the AP would be doing the auth and not the switch)
- The PCAP from the AP doesn't seem to have any responses.
- The PCAP from the engine shows the auth packets coming in, I would expect to see packets going to the NPS servers but nothing is there.
- This makes me think the authentication is no longer forwarding.
- I'm unsure where to look to troubleshoot this (or if that's expected behavior for some reason)
- The NPS servers have no auth request events from me.
I'm happy to learn more and give details on anything but I'm currently going around in circles and assume I'm not aware of or overlooking something.
Thank you.
0 REPLIES 0