- Extreme Networks
- Community List
- Network Management & Authentication
- ExtremeCloud IQ- Site Engine Management Center
- Re: Cisco Trunk Interface with Extreme NAC
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Cisco Trunk Interface with Extreme NAC
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Get Direct Link
- Report Inappropriate Content
10-12-2020 07:33 AM
Dear All
I’m trying to enable Extreme NAC for Cisco switches. It works fine for Clients on Access Ports. For Accesspoints (local breakout), I’m trying to get a trunk interface with management vlan untagged and data VLANs tagged.
For XOS Switches, I would create a Role with the needed VLAN Egress config
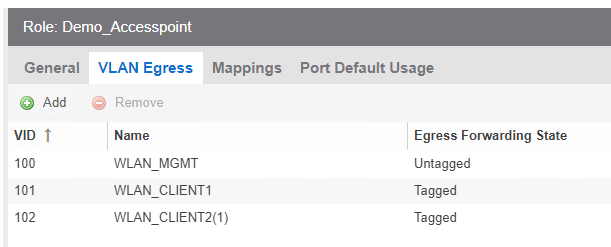
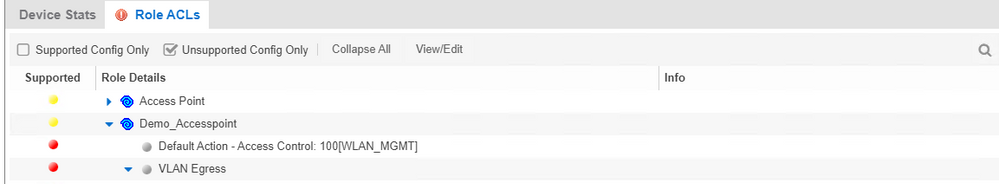
But I cant enforce this role configuration to Cisco switches
How can I achieve that for Cisco switches with Extreme NAC?
Solved! Go to Solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Get Direct Link
- Report Inappropriate Content
10-15-2020 11:53 AM
Hi Miguel
Yes sure, I can share my cisco config. In the meantime, I tested NEAT as well and it seems to be easier than using macro.
Macro
conf t
no macro auto global control device
no macro auto global control trigger
macro auto global processing
macro auto execute AP_TRUNK {
if [[ $LINKUP == YES ]]
then conf t
default interface $INTERFACE
interface $INTERFACE
Description AP_TRUNK
macro description $TRIGGER
switchport trunk allowed vlan ##VLAN-LIST##
switchport trunk native vlan ##VLAN##
switchport mode trunk
spanning-tree portfast trunk
macro auto processing
exit
fi
if [[ $LINKUP == NO ]]
then conf t
default interface $INTERFACE
interface $INTERFACE
description NAC
no switchport trunk allowed vlan
no switchport trunk native vlan
switchport mode access
macro auto processing
authentication control-direction in
authentication event server dead action authorize
authentication event server dead action authorize voice
authentication event server alive action reinitialize
authentication host-mode multi-host
authentication order mab dot1x
authentication priority dot1x mab
authentication port-control auto
authentication periodic
authentication timer reauthenticate server
authentication violation restrict
mab
snmp trap mac-notification change added
snmp trap mac-notification change removed
dot1x pae authenticator
dot1x timeout tx-period 10
no macro description $TRIGGER
exit
fi
}
int range ##INTERFACE-RANGE##
macro auto processing
Radius Attribute: Cisco-AVPair=auto-smart-port=AP_TRUNK
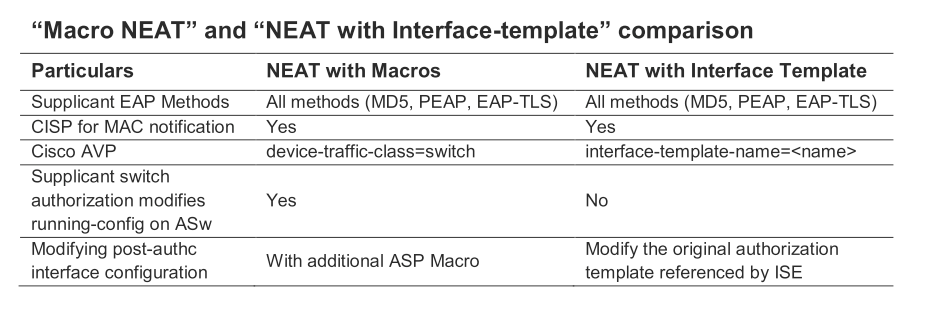
NEAT
cisp enable
!
template AP_TRUNK
switchport trunk encapsulation dot1q
switchport trunk native vlan 100
switchport mode trunk
Radius Attribute: Cisco-AVPair=interface-template-name=AP_TRUNK
Comparison Smart Port vs. Macro:
best regards
Michael
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Get Direct Link
- Report Inappropriate Content
10-13-2020 06:16 AM
Thanks for your replys.
So my first step is to get it running to convert a port from access to trunk. Dynamic VLAN is my next stept.
Based on the documentation, I did following configuration.
Radius attribute configuration:

Policy mapping:
Set the custom 1

The result is that in the “End-Systems” tab it looks fine with the defined attributes (cisco-av-pair is set correctly)

the config evaluation tool looks fine as well

But on the switch the interface remains as access port. So I did a debug on the switch and a tcp dump on the NAC engine. In both of them, I can’t see this atrribute.
Tcp Dump NAC Engine
root@itbzs951:~$ tcpdump "host 172.16.1.99" -v
tcpdump: listening on eth0, link-type EN10MB (Ethernet), capture size 262144 bytes
08:11:14.080546 IP (tos 0x0, ttl 253, id 45515, offset 0, flags [none], proto UDP (17), length 286)
172.16.1.99.datametrics > itbzs951.rzb.ch.radius: RADIUS, length: 258
Access-Request (1), id: 0x4f, Authenticator: 685e68a2ba54bbdba948fcb175c862d5
User-Name Attribute (1), length: 14, Value: 008077515afa
User-Password Attribute (2), length: 18, Value:
Service-Type Attribute (6), length: 6, Value: Call Check
Vendor-Specific Attribute (26), length: 31, Value: Vendor: Cisco (9)
Vendor Attribute: 1, Length: 23, Value: service-type=Call Check
Framed-MTU Attribute (12), length: 6, Value: 1500
Called-Station-Id Attribute (30), length: 19, Value: 34-F8-E7-C4-01-83
Calling-Station-Id Attribute (31), length: 19, Value: 00-80-77-51-5A-FA
Message-Authenticator Attribute (80), length: 18, Value: .Q......c.H.....
Unknown Attribute (102), length: 2, Value:
Vendor-Specific Attribute (26), length: 49, Value: Vendor: Cisco (9)
Vendor Attribute: 1, Length: 41, Value: audit-session-id=AC1001630000009C7FB1A5B2
Vendor-Specific Attribute (26), length: 18, Value: Vendor: Cisco (9)
Vendor Attribute: 1, Length: 10, Value: method=mab
NAS-IP-Address Attribute (4), length: 6, Value: 172.16.1.99
NAS-Port-Id Attribute (87), length: 20, Value: GigabitEthernet0/3
NAS-Port-Type Attribute (61), length: 6, Value: Ethernet
NAS-Port Attribute (5), length: 6, Value: 50103
08:11:14.128037 IP (tos 0x0, ttl 64, id 57966, offset 0, flags [none], proto UDP (17), length 65)
itbzs951.rzb.ch.radius > 172.16.1.99.datametrics: RADIUS, length: 37
Access-Accept (2), id: 0x4f, Authenticator: 9c553fbf49b3d282e6125af6c230c862
Tunnel-Type Attribute (64), length: 6, Value: Tag[Unused] VLAN
Tunnel-Private-Group-ID Attribute (81), length: 5, Value: 999
Tunnel-Medium-Type Attribute (65), length: 6, Value: Tag[Unused] 802
08:11:15.170597 IP (tos 0x0, ttl 253, id 45526, offset 0, flags [none], proto UDP (17), length 252)
172.16.1.99.sa-msg-port > itbzs951.rzb.ch.radius-acct: RADIUS, length: 224
Accounting-Request (4), id: 0x5e, Authenticator: 390556e6c058ae69e9f8e4daa2ee3993
User-Name Attribute (1), length: 14, Value: 008077515afa
Vendor-Specific Attribute (26), length: 49, Value: Vendor: Cisco (9)
Vendor Attribute: 1, Length: 41, Value: audit-session-id=AC1001630000009C7FB1A5B2
Vendor-Specific Attribute (26), length: 19, Value: Vendor: Cisco (9)
Vendor Attribute: 1, Length: 11, Value: vlan-id=999
Vendor-Specific Attribute (26), length: 18, Value: Vendor: Cisco (9)
Vendor Attribute: 1, Length: 10, Value: method=mab
Called-Station-Id Attribute (30), length: 19, Value: 34-F8-E7-C4-01-83
Calling-Station-Id Attribute (31), length: 19, Value: 00-80-77-51-5A-FA
NAS-IP-Address Attribute (4), length: 6, Value: 172.16.1.99
NAS-Port-Id Attribute (87), length: 20, Value: GigabitEthernet0/3
NAS-Port-Type Attribute (61), length: 6, Value: Ethernet
NAS-Port Attribute (5), length: 6, Value: 50103
Acct-Session-Id Attribute (44), length: 10, Value: 00000071
Acct-Status-Type Attribute (40), length: 6, Value: Start
Event-Timestamp Attribute (55), length: 6, Value: Tue Oct 13 08:11:15 2020
Acct-Delay-Time Attribute (41), length: 6, Value: 00 secs
08:11:15.171425 IP (tos 0x0, ttl 64, id 58193, offset 0, flags [none], proto UDP (17), length 48)
itbzs951.rzb.ch.radius-acct > 172.16.1.99.sa-msg-port: RADIUS, length: 20
Accounting-Response (5), id: 0x5e, Authenticator: 9268a78ff22e9f4a1253178622130e1c
Debug Switch:
Oct 13 08:11:13.165: dot1x-ev:[Gi0/3] Interface state changed to UP
Oct 13 08:11:13.169: dot1x-ev:DOT1X Supplicant not enabled on GigabitEthernet0/3
Oct 13 08:11:13 UTC+1: %LINK-3-UPDOWN: Interface GigabitEthernet0/3, changed state to up
Oct 13 08:11:14.070: AAA/AUTHEN/8021X (00000000): Pick method list 'default'
Oct 13 08:11:14.070: AAA/AUTHEN(00000000): There is no General DBReply Method Index details may not be specified
Oct 13 08:11:14.070: RADIUS/ENCODE(00000000):Orig. component type = Invalid
Oct 13 08:11:14.070: RADIUS/ENCODE(00000000): Unsupported AAA attribute hwidb
Oct 13 08:11:14.070: RADIUS/ENCODE(00000000): Unsupported AAA attribute auth-profile
Oct 13 08:11:14.070: RADIUS/ENCODE(00000000): Unsupported AAA attribute aaa-authen-type
Oct 13 08:11:14.070: RADIUS/ENCODE(00000000): Unsupported AAA attribute aaa-authen-service
Oct 13 08:11:14.070: RADIUS/ENCODE(00000000): Unsupported AAA attribute clid-mac-addr
Oct 13 08:11:14.070: RADIUS/ENCODE(00000000): Unsupported AAA attribute target-scope
Oct 13 08:11:14.070: RADIUS/ENCODE(00000000): Unsupported AAA attribute aaa-unique-id
Oct 13 08:11:14.070: RADIUS(00000000): Config NAS IP: 0.0.0.0
Oct 13 08:11:14.070: RADIUS(00000000): Config NAS IPv6: ::
Oct 13 08:11:14.070: RADIUS(00000000): sending
Oct 13 08:11:14.070: RADIUS/ENCODE: Best Local IP-Address 172.16.1.99 for Radius-Server 192.168.105.6
Oct 13 08:11:14.070: RADIUS: Message Authenticator encoded
Oct 13 08:11:14.070: RADIUS(00000000): Send Access-Request to 192.168.105.6:1812 onvrf(0) id 1645/79, len 258
Oct 13 08:11:14.070: RADIUS: authenticator 68 5E 68 A2 BA 54 BB DB - A9 48 FC B1 75 C8 62 D5
Oct 13 08:11:14.070: RADIUS: User-Name [1] 14 "008077515afa"
Oct 13 08:11:14.070: RADIUS: User-Password [2] 18 *
Oct 13 08:11:14.070: RADIUS: Service-Type [6] 6 Call Check [10]
Oct 13 08:11:14.074: RADIUS: Vendor, Cisco [26] 31
Oct 13 08:11:14.074: RADIUS: Cisco AVpair [1] 25 "service-type=Call Check"
Oct 13 08:11:14.074: RADIUS: Framed-MTU [12] 6 1500
Oct 13 08:11:14.074: RADIUS: Called-Station-Id [30] 19 "34-F8-E7-C4-01-83"
Oct 13 08:11:14.074: RADIUS: Calling-Station-Id [31] 19 "00-80-77-51-5A-FA"
Oct 13 08:11:14.074: RADIUS: Message-Authenticato[80] 18
Oct 13 08:11:14.074: RADIUS: F0 51 02 09 AD CE DA 95 63 8A 48 91 D1 86 94 F7 [ QcH]
Oct 13 08:11:14.074: RADIUS: EAP-Key-Name [102] 2 *
Oct 13 08:11:14.074: RADIUS: Vendor, Cisco [26] 49
Oct 13 08:11:14.074: RADIUS: Cisco AVpair [1] 43 "audit-session-id=AC1001630000009C7FB1A5B2"
Oct 13 08:11:14.074: RADIUS: Vendor, Cisco [26] 18
Oct 13 08:11:14.074: RADIUS: Cisco AVpair [1] 12 "method=mab"
Oct 13 08:11:14.074: RADIUS: NAS-IP-Address [4] 6 172.16.1.99
Oct 13 08:11:14.074: RADIUS: NAS-Port-Id [87] 20 "GigabitEthernet0/3"
Oct 13 08:11:14.074: RADIUS: NAS-Port-Type [61] 6 Ethernet [15]
Oct 13 08:11:14.074: RADIUS: NAS-Port [5] 6 50103
Oct 13 08:11:14.074: RADIUS(00000000): Sending a IPv4 Radius Packet
Oct 13 08:11:14.074: RADIUS(00000000): Started 1 sec timeout
Oct 13 08:11:14.123: RADIUS: Received from id 1645/79 192.168.105.6:1812, Access-Accept, len 37
Oct 13 08:11:14.123: RADIUS: authenticator 9C 55 3F BF 49 B3 D2 82 - E6 12 5A F6 C2 30 C8 62
Oct 13 08:11:14.123: RADIUS: Tunnel-Type [64] 6 00:VLAN [13]
Oct 13 08:11:14.123: RADIUS: Tunnel-Private-Group[81] 5 "999"
Oct 13 08:11:14.123: RADIUS: Tunnel-Medium-Type [65] 6 00:ALL_802 [6]
Oct 13 08:11:14.123: RADIUS(00000000): Received from id 1645/79
Oct 13 08:11:14 UTC+1: %EPM-6-POLICY_REQ: IP 0.0.0.0| MAC 0080.7751.5afa| AuditSessionID AC1001630000009C7FB1A5B2| EVENT APPLY
Oct 13 08:11:14 UTC+1: %LINEPROTO-5-UPDOWN: Line protocol on Interface GigabitEthernet0/3, changed state to up
Oct 13 08:11:15.161: RADIUS/ENCODE(00000000):Orig. component type = Invalid
Oct 13 08:11:15.161: RADIUS/ENCODE(00000000): Unsupported AAA attribute clid-mac-addr
Oct 13 08:11:15.161: RADIUS(00000000): Config NAS IP: 0.0.0.0
Oct 13 08:11:15.161: RADIUS(00000000): Config NAS IPv6: ::
Oct 13 08:11:15.161: RADIUS(00000000): sending
Oct 13 08:11:15.161: RADIUS/ENCODE: Best Local IP-Address 172.16.1.99 for Radius-Server 192.168.105.6
Oct 13 08:11:15.161: RADIUS(00000000): Send Accounting-Request to 192.168.105.6:1813 onvrf(0) id 1646/94, len 224
Oct 13 08:11:15.161: RADIUS: authenticator 39 05 56 E6 C0 58 AE 69 - E9 F8 E4 DA A2 EE 39 93
Oct 13 08:11:15.161: RADIUS: User-Name [1] 14 "008077515afa"
Oct 13 08:11:15.161: RADIUS: Vendor, Cisco [26] 49
Oct 13 08:11:15.161: RADIUS: Cisco AVpair [1] 43 "audit-session-id=AC1001630000009C7FB1A5B2"
Oct 13 08:11:15.165: RADIUS: Vendor, Cisco [26] 19
Oct 13 08:11:15.165: RADIUS: Cisco AVpair [1] 13 "vlan-id=999"
Oct 13 08:11:15.165: RADIUS: Vendor, Cisco [26] 18
Oct 13 08:11:15.165: RADIUS: Cisco AVpair [1] 12 "method=mab"
Oct 13 08:11:15.165: RADIUS: Called-Station-Id [30] 19 "34-F8-E7-C4-01-83"
Oct 13 08:11:15.165: RADIUS: Calling-Station-Id [31] 19 "00-80-77-51-5A-FA"
Oct 13 08:11:15.165: RADIUS: NAS-IP-Address [4] 6 172.16.1.99
Oct 13 08:11:15.165: RADIUS: NAS-Port-Id [87] 20 "GigabitEthernet0/3"
Oct 13 08:11:15.165: RADIUS: NAS-Port-Type [61] 6 Ethernet [15]
Oct 13 08:11:15.165: RADIUS: NAS-Port [5] 6 50103
Oct 13 08:11:15.165: RADIUS: Acct-Session-Id [44] 10 "00000071"
Oct 13 08:11:15.165: RADIUS: Acct-Status-Type [40] 6 Start [1]
Oct 13 08:11:15.165: RADIUS: Event-Timestamp [55] 6 1602569475
Oct 13 08:11:15.165: RADIUS: Acct-Delay-Time [41] 6 0
Oct 13 08:11:15.165: RADIUS(00000000): Sending a IPv4 Radius Packet
Oct 13 08:11:15.165: RADIUS(00000000): Started 1 sec timeout
Oct 13 08:11:15.168: RADIUS: Received from id 1646/94 192.168.105.6:1813, Accounting-response, len 20
Oct 13 08:11:15.168: RADIUS: authenticator 92 68 A7 8F F2 2E 9F 4A - 12 53 17 86 22 13 0E 1C
For me it looks like the NAC engine doesn’t sent the attribute but the attribute is shown in the dashboard.
regards
Michael
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Get Direct Link
- Report Inappropriate Content
10-12-2020 12:19 PM
Hello Michael,
there is a official Extreme Guide for the integration of Cisco into XMC and NAC.
Please see here:
Regards
Stephan
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Get Direct Link
- Report Inappropriate Content
10-12-2020 11:08 AM
Michael,
For Cisco switches to understand the dynamic VLAN provisioning there is some more things to do.
Have a look here:
- https://community.cisco.com/t5/security-documents/neat-with-interface-template/ta-p/3642967
- https://www.cisco.com/c/en/us/support/docs/wireless/wireless-lan-controller-software/200492-Securing...
- https://community.cisco.com/t5/wireless-security-and-network/flexconnect-ap-dynamic-vlan-and-local-c...
As you’ll see this part is specific to Cisco equipment.
On the Extreme side you’ll have to send this (aligned with your config):

There is some more work ...
Mig
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Get Direct Link
- Report Inappropriate Content
10-12-2020 08:58 AM
Hi Miguel
I understand that I have do do it via Radius attribute. But I don’t understand where I can define the native (untagged) and the list of allowed vlans.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Get Direct Link
- Report Inappropriate Content
10-12-2020 07:44 AM
Michael,
For cisco switches you cannot enforce a Role from the policy domain.
You must send standard and Cisco radius attributes only.
The standards are those in the Policy Mapping and the cisco specific are to be defined via the Custom/Organization fields in Policy Mapping and/or via the “configure device/Radius attributes to send” from the switch in the NAC group Engine:


Mig

