- Extreme Networks
- Community List
- Switching & Routing
- ExtremeSwitching (EXOS/Switch Engine)
- Re: EXOS Packet Capture
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
EXOS Packet Capture
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Get Direct Link
- Report Inappropriate Content
05-18-2021 01:00 PM
Hello,
today I played around with the built-in packet capture of EXOS ( How To: How to perform a local packet capture on an EXOS switch | Extreme Portal (force.com) )
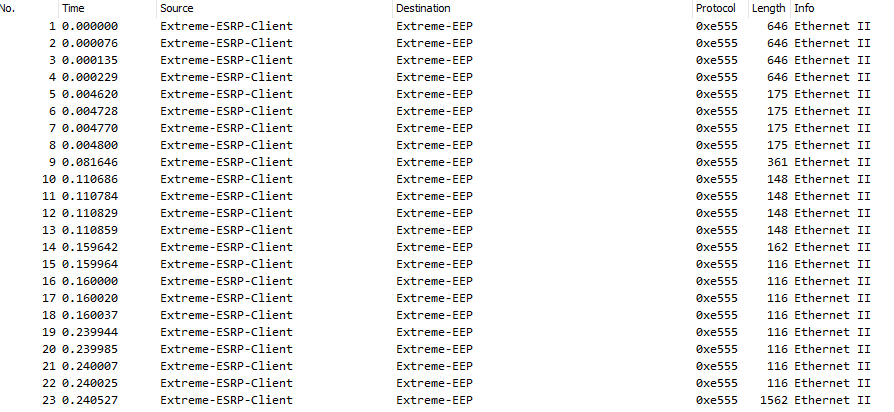
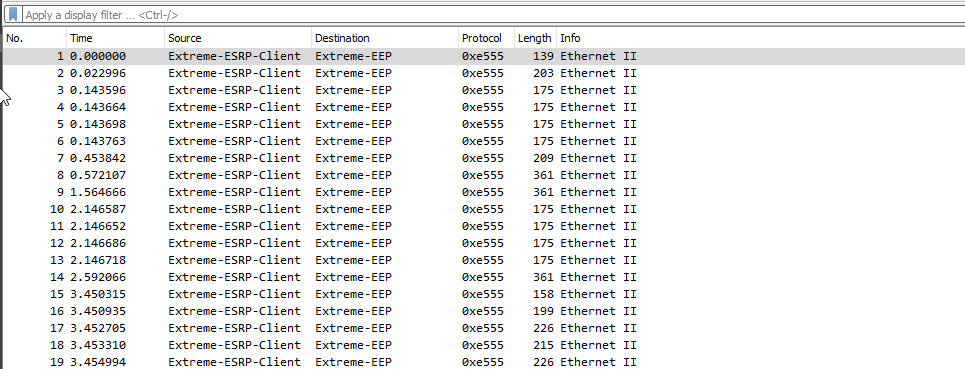
I’m able to capture packets and open the pcap file with wireshark, but I only see the following packets:
Wondering if I’m doing something wrong or if the feature is something else than I’m thinking. Any hints?
Best regards
Stefan
Solved! Go to Solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Get Direct Link
- Report Inappropriate Content
05-18-2021 03:54 PM
Hi,
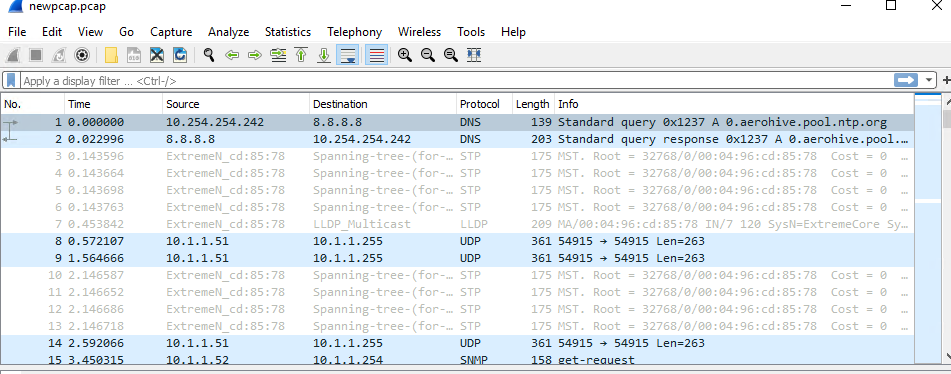
You can use the editcap tool to remove the first 52 bytes. Mine looked something like below from Powershell:
PS C:\Program Files\Wireshark> .\editcap.exe -C 52 editcap.pcap newpcap.pcap
syntax below:
PS C:\Program Files\Wireshark> .\editcap.exe -C 52 <original pcap filename> <new pcap filename>Below is more on editcap:
https://www.wireshark.org/docs/man-pages/editcap.html
Before:
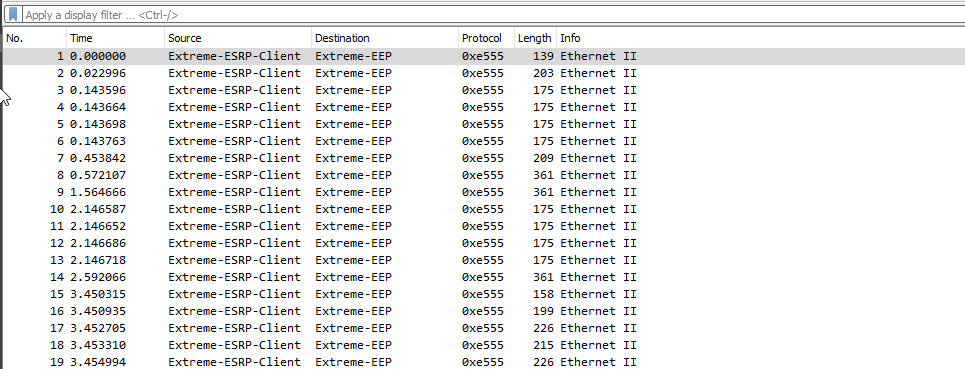
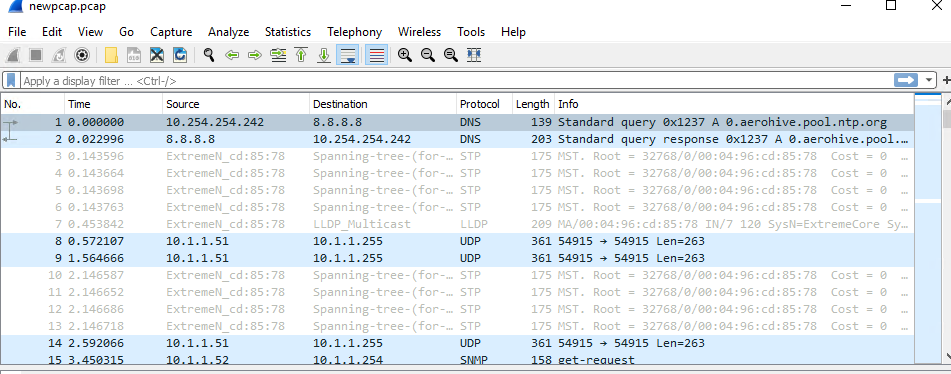
After:
Thanks,
Chris Thompson
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Get Direct Link
- Report Inappropriate Content
05-18-2021 05:51 PM
Hi Stefan,
You bring upa good point(Stefan 1, Chris 0) so that article has been updated:
How To: How to perform a local packet capture on an EXOS switch | Extreme Portal (force.com)
Thanks again,
Chris Thompson
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Get Direct Link
- Report Inappropriate Content
05-18-2021 05:13 PM
Hi Chris,
this worked like a charm, thank you very much! How much “trouble” some 52 bytes can cause… 🙂
Maybe this little information can be added to the GTAC articles?
Best regards
Stefan
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Get Direct Link
- Report Inappropriate Content
05-18-2021 03:54 PM
Hi,
You can use the editcap tool to remove the first 52 bytes. Mine looked something like below from Powershell:
PS C:\Program Files\Wireshark> .\editcap.exe -C 52 editcap.pcap newpcap.pcap
syntax below:
PS C:\Program Files\Wireshark> .\editcap.exe -C 52 <original pcap filename> <new pcap filename>Below is more on editcap:
https://www.wireshark.org/docs/man-pages/editcap.html
Before:
After:
Thanks,
Chris Thompson
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Get Direct Link
- Report Inappropriate Content
03-17-2026 09:56 AM - edited 03-17-2026 09:57 AM
From what you described, it sounds like the packet capture itself is working, since you’re able to export the pcap file and open it in Wireshark. When only a limited or unusual set of packets appears, Flixer it’s often related to where the capture is attached or what traffic actually passes through that point on the switch.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Get Direct Link
- Report Inappropriate Content
03-16-2026 10:31 AM - edited 03-16-2026 10:31 AM
from what you’re describing, it doesn’t sound like you’re doing anything wrong—it’s more about how the EXOS packet capture feature actually works under the hood. Flixtor The built-in capture on EXOS switches is fairly limited compared to something like a full span/mirror session feeding into Wireshark.
In many cases, EXOS captures are restricted to CPU-bound traffic (control plane) rather than full data plane forwarding. That means you’ll mostly see things like ARP, LLDP, STP, or other management/control packets, which would explain why your capture looks “incomplete” or not what you expected.
